The software / hardware inventory functionality provides a complete, searchable hardware, software, patch and virtual-machine inventory along with the ability to issue alerts when software is (un)installed, or when applications register themselves in certain registry keys. Combined with Service Monitoring and File Monitoring, EventSentry will detect the majority of changes made to system.
 Virtual Machine Inventory (Hyper-V, Proxmox & VMWare)
Virtual Machine Inventory (Hyper-V, Proxmox & VMWare)
Inventories all virtual machines from Hyper-V, Proxmox or VMWare hosts as well as the version number of the virtual machine host. Hyper-V inventory is automatically retrieved when Hyper-V is detected on the host where the EventSentry agent is running. Proxmox inventory information is obtained via SSH, VMWare inventory information via SNMP when the required SNMP OIDs exist. The following information is available:
Virtual Machine Host
•Host Name
•Product Name
•Product Version
Virtual Machines
•Host Name
•Status
•CPU Count
•Memory
•Operating System (if available)
|
Proxmox inventory requires that SSH credentials are configured, VMWare inventory requires that SNMP is enabled on the VMWare ESXi hosts. |
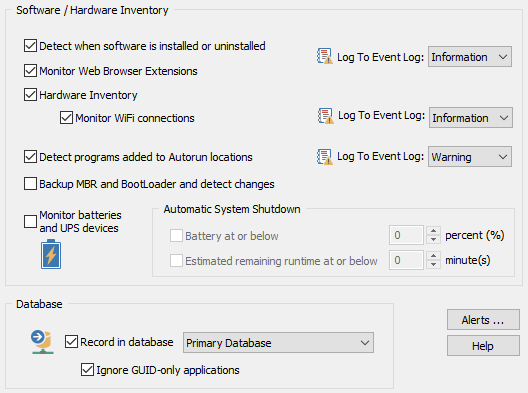
Monitor WiFi Connections
Tracks all WiFi activity and shows which Wireless network an adapter is connected to along with a history of all connections and disconnections. The EventSentry agent will also log events to the event log every time an adapter connects or disconnects from a WiFi network, which allows for automation using filters.
The following details are available:
•Adapter Name & GUID
•Status
•Signal Strength
•SSID
•Cipher (e.g. RSNA with PSK)
•Authentication (e.g. CCMP)
Monitoring Batteries & UPS Devices
Monitors built-in batteries in laptops as well as attached UPS devices (if detected by Windows). The current battery status, charge level as well as the total battery capacity are available on the "Host / Inventory" page in the web-based reporting. EventSentry can also shut down a host if the battery status falls below a configurable percent threshold or when the estimated runtime is less than a preset limit, irrespective of the UPS manufacturer and/or model.
Backup MBR and BootLoader and detect changes
Downloads sectors 0-77 as well the sectors 2048-2057 of all hard drives on the monitored system. If changes are detected on the monitored sectors, an event is logged indicating how many bytes were changed and whether the MBR or BootLoader were changed. All monitored sectors are also stored in the database when the agent starts (if enabled) and can be downloaded on the "Host / Inventory" page in the web-based reporting.
|
This feature is intended to provide some protection against certain Ransomware infections. The events logged when monitored sectors are changed can be used to trigger actions like hibernation, a logoff or a shutdown. The sector backups can be downloaded to a USB boot disk and restored manually in case the original sectors have been overwritten inadvertently. |
Software Inventory
If an application is installed an registers itself in the Control Panel under Add/Remove Programs, then EventSentry will notify you and log which application was installed or removed.
If an application does not register itself in Add/Remove Programs, for example if it is installed on a per-user basis, then EventSentry will not detect it. You might still be notified if the application registers itself in one of the many autorun registry keys.
The following information is stored in the database and can be queried using the web reports when the "Record in database" check box is checked:
•Software Name
•Installation Directory*
•Software Publisher*
•Software Version*
•Platform Information (32-bit vs 64-bit)
This feature will also write application history to the database, enabling you to find out when software was installed/uninstalled (note that this information might also be available through the event logs).
Monitoring Web Browser Extensions
Monitor all installed extensions for the following web browsers
•Mozilla Firefox
•Google Chrome
•Microsoft Edge (chromium-based)
and provides a full inventory/history as well alerts when extensions are installed or uninstalled. Browser profiles are supported as well. The following extension information is captured:
•Name
•Publisher
•Version
•Enabled/Disabled
•Publisher (when available)
•Username
Please see below for limitations of this feature since there is no official standard on how browser extensions are stored.
|
•Under some circumstances the extension name may not be displayed, in which case the publisher is shown instead. •An extension will show up as enabled if it is installed in multiple profiles and enabled in at least one profile. |
Patch Inventory
All installed Microsoft patches are collected and can be queried through the web reports. EventSentry can also issue alerts when a patch is (un)installed. The following information is available:
•Patch Name
•Platform Information (32-bit vs 64-bit)
•Installation Date
•Installation Directory (if applicable)
•Publisher
The following hardware information is captured; Hardware information is obtained through file information, registry data and WMI.
•Operating System, including Edition and Service Pack
•The location of the SYSTEMROOT directory
•Date when the Operating System was installed
•Whether the machine is running the x64-bit edition of the OS
•Configured UAC level (Vista and later)
•Whether the machine is a Terminal Server, running Hyper-V or Server-Core
•If the machine is a virtual machine, and in some cases the type of VM platform (e.g. VMWare ESX)
•Installed CPU's (including type, speed and number of CPU's installed)**
•The number of installed CPUs, including Hyper-Threading and multi-core detection
•Registered owner and registered company** (if available)
•Computer manufacturer and model** (if available)
•Chassis type (e.g. rack-mount, mini tower, laptop, etc.)
•Warranty information (DELL, HP, IBM & Lenovo hardware only)
•BIOS Version***
•Serial Number, Service Tag (depending on manufacturer)***
•Installed Memory, including the maximum memory, number of memory chips installed and free slots available
•Installed network adapters, including adapter name, link speed, IP address (updated & refreshed periodically) and MAC address
•Installed disk controllers, including adapter name, adapter type (IDE/SCSI) and manufacturer
•Make of installed graphics adapter
•The number of CD-ROM, DVD, Floppy and removable drives
•The current uptime
•The maximum uptime of the host since EventSentry was installed
•Highest supported USB version
•Attached keyboards (logs event 12048)
|
Basic system and hardware information can also be obtained via SNMP from a remote SNMP agent by polling SNMP counter values. This includes (when available):
•System Information •Network Interfaces •Processor, memory & disk space information •Uptime information
Extended hardware information is available when SSH credentials are configured:
•Time zone •USB version •OS Install Date •Manufacturer details •Additional CPU details
The Heartbeat Agent retrieves data from Non-Windows hosts via SNMP and/or SSH. |
On DELL© and HP© servers with the appropriate vendor system management tools installed, EventSentry will also collect the following information when installed:
•Status of redundant power supplies (PSUs)
•Current temperature of installed temperature sensors
•Current status and RPM of installed fans
•Availability and IP address of any installed remote management cards
•Status and details of any installed hardware RAID controller (e.g. model number, cache size, firmware version)
•Status of all configured RAIDs (including stripe size (when available), status, raid level)
•Status of all installed physical hard drives, including drive details such as model number, serial number
|
HP GEN 10+ SERVERS: Starting with its generation 10, obtaining managed hardware info from HP servers - with the exception of physical disk (raid) information - requires an iLO card that does not share the same network interface as the Windows OS.
Since iLO cards require authentication, two variables will need to be set on the host(s) or group(s) of servers with Gen 10 iLO cards:
HPILOUSER iLO User HPILOPASS Password |
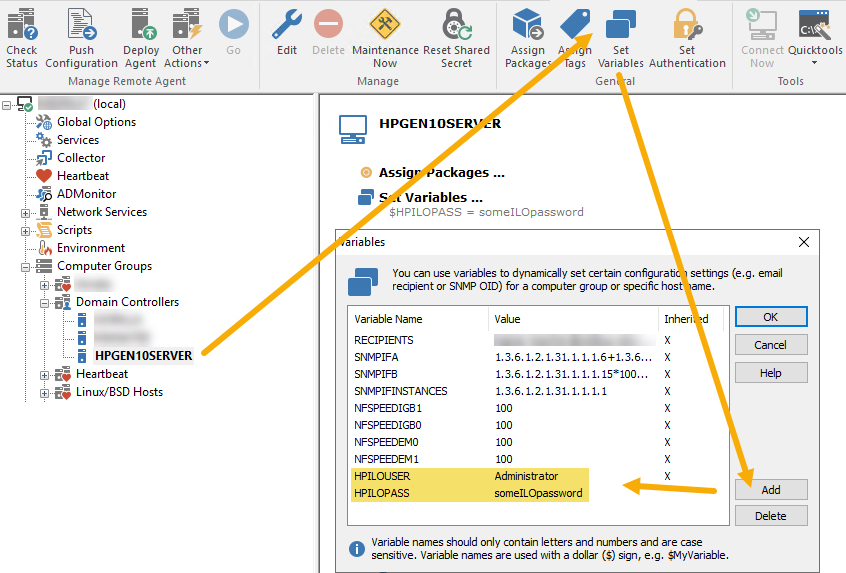
Setting a variable to access a HP Gen10 iLO
Upon agent start, the hardware inventory feature can also log an event to the event log if the number of the following installed hardware devices changes since the last time the EventSentry agent was running:
•Installed Memory
•Number of installed processors
•Number of installed floppy drives
•Number of installed CDROM drives
•Number of installed DVD drives
•Number of removable drives
•Link speed of a network adapter
•Addition / Removal of a USB drive
•S.M.A.R.T. status error of a physical drive
Ignore GUID-only applications: Some software will write only the GUID (a hexadecimal number) to the registry when installed. Check this box to ignore software without a useful display name.
|
System hardware information is updated every time the EventSentry service is started. |
The current uptime of a host is refreshed every 5 minutes and provides the following functionality:
•Keeps track of the maximum uptime across multiple reboots. This can help isolate problematic servers that are rebooted often
•Stores uptime history in the database, which can be accessed through Heartbeat - Availability - Uptime History. The uptime history is updated every time the OS is booting, and records how long the OS was running before the current boot process.
The uptime history keeps track of how long the OS was running between reboots and is only updated when you reboot a host.
Autorun Registry Keys
Some applications register files to automatically run when the computer starts or when a user logs on to the system. While those files are usually required and harmless, this is unfortunately misused by Spyware, Trojan horses and viruses.
EventSentry monitors certain registry locations and will notify you when an application is added or removed from one of the monitored locations. Please note that only HKEY_LOCAL_MACHINE registry keys, which affect all users on the system, are monitored at this time. HKEY_CURRENT_USER keys are not monitored.
EventSentry monitors the following registry values:
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Taskman
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows\AppInit_DLLs
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\Shell
EventSentry monitors the following registry keys:
HKLM\SOFTWARE\Microsoft\Active Setup\Installed Components
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnceEx
HKLM\SOFTWARE\Policies\Microsoft\Windows\System\Scripts\Startup
HKLM\SOFTWARE\Policies\Microsoft\Windows\System\Scripts\Logon
Autorun Directories
In addition to the registry keys listed above, this feature will also monitor the following directories and notify you if a file is added:
<Documents and Settings>\All Users\Start Menu\Programs\Startup
Additional Information
The Active Setup\Installed Components registry subkey is intended to be used by installations to make sure that all users on a system have up-to-date information in their profile, and as such is examined every time a user logs in. This key has unfortunately been misused by software to install and run malicious applications. We urge you to investigate all changes to this registry key to make sure only authorized applications register themselves there.
Please see the next chapter for all event records logged to the application event log by this feature.
* The amount of information recorded by EventSentry depends on the information provided by the installation routine of the particular software. It is up to the software vendor to determine how much installation they will record in the registry. Most modern software will log the name, publisher and version of the application installed.
** Some information might not be available. Model and manufacturer is available on most pre-installed computers; registered company is only available if specified during installation; in some cases CPU's information (especially older models) will not show the CPU type.


