Detecting Emotet malware with Emocheck and EventSentry
Emotet (https://en.wikipedia.org/wiki/Emotet) is dangerous malware that has been infecting networks since 2016, causing serious damage to organizations. The team of JPCERT created Emocheck, a command line utility that detects running emotet processes.
This article explains how to configure EvenSentry to run emocheck and trigger an email when the tool detects a threat.
Creating an embedded script in EventSentry
Deploying the tool using EventSentry Admin Assistant
Since emocheck needs to be executed on every host that could potentially be infected, emocheck needs to either be run from a central file share or be executed locally. Since setting up a file share (and the appropriate permissions) is beyond the scope of EventSentry, we’ll cover copying the file to the remote hosts with the EventSentry Admin Assistant here. Of course you can also utilize other software deployment methods or scripts to get the emocheck executable to the remote hosts.
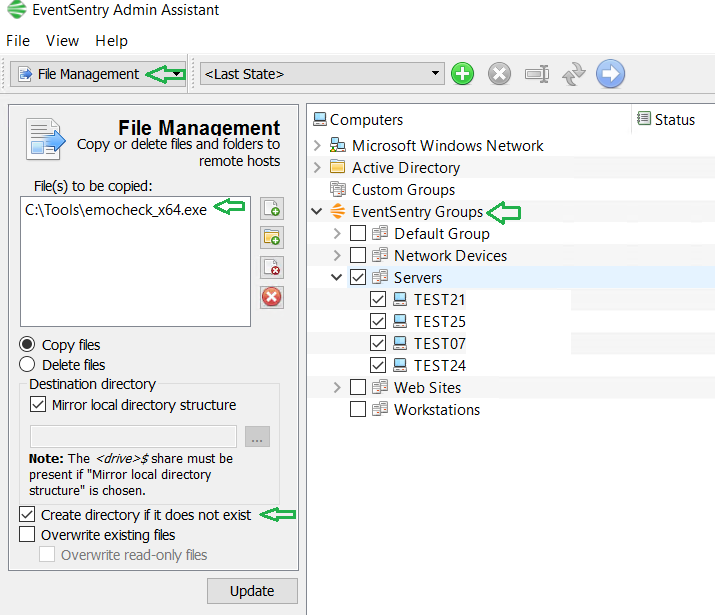
After installing the EventSentry Admin Assistant, open the app and choose "File Management" from action menu. There, add the emocheck_x64.exe executable to the list (Note that the filename could change depends of the version, for example "emocheck_v2.0_x64.exe", we recommend to rename the version filename to emocheck_x64.exe), select "Mirror local directory" (assuming that we keep the same directory structure from where we are deploying the files from) and select "Create directory if it does not exist". There are several options to select the computers to which the executable is copied to, including local network (discovery), Active Directory and EventSentry Groups. Remember that this tool must be running under a user with enough access rights to copy the file to the computers on the network.
Fig.1: Admin Asistant Tool - Pushing files computers
Note: Filename could be different based on version number.
Creating an Embedded Script in the EventSentry Management Console
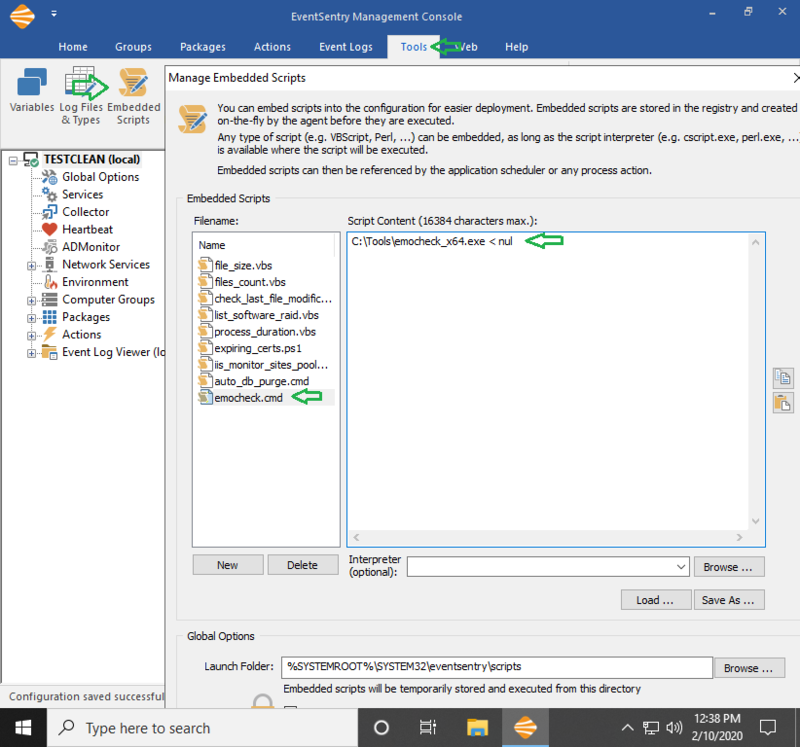
In the Tools menu of the EventSentry Management Console, select Embedded Scripts and click the New button. Give the script a descriptive name (e.g. emocheck.cmd) and specify the script content. Since the tool was copied to all computers from and to the C:\Tools directory, specify
C:\Tools\emocheck_x64.exe < nul as the content (Note: The trailing " < nul" at the end of the command line is necessary since the emocheck tool will not exit until a key is pressed) and click OK.
Fig.2: Manage Embedded Scripts
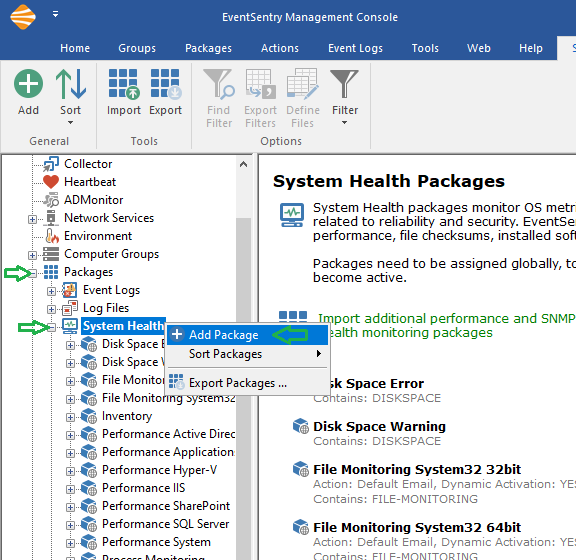
Creating a System Health Package with an Application Scheduler
The next step is to create a system health package with an application scheduler object, which can run any script in preset intervals or times. Expand Packages in the management console, right-click System Health and click Add Package. Give the package a descriptive name, e.g. "Emocheck".
Fig.3: Creating System Health Package
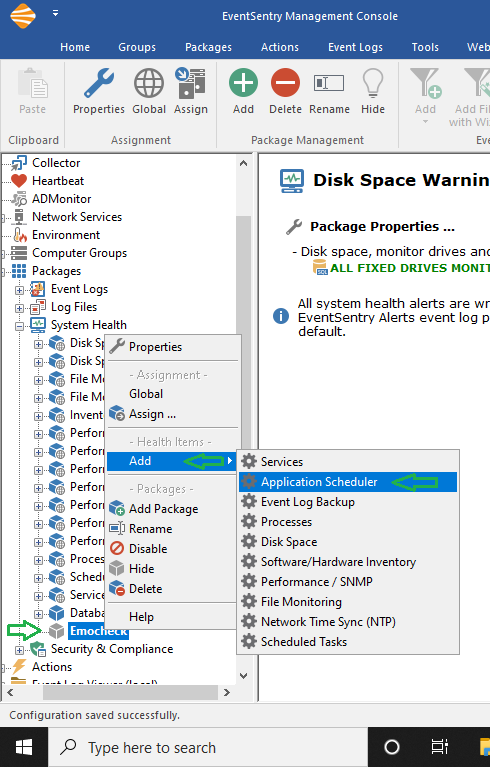
Then, right-click the new package and add an Application Scheduler object as shown below.
Fig.4: Adding Application Scheduler
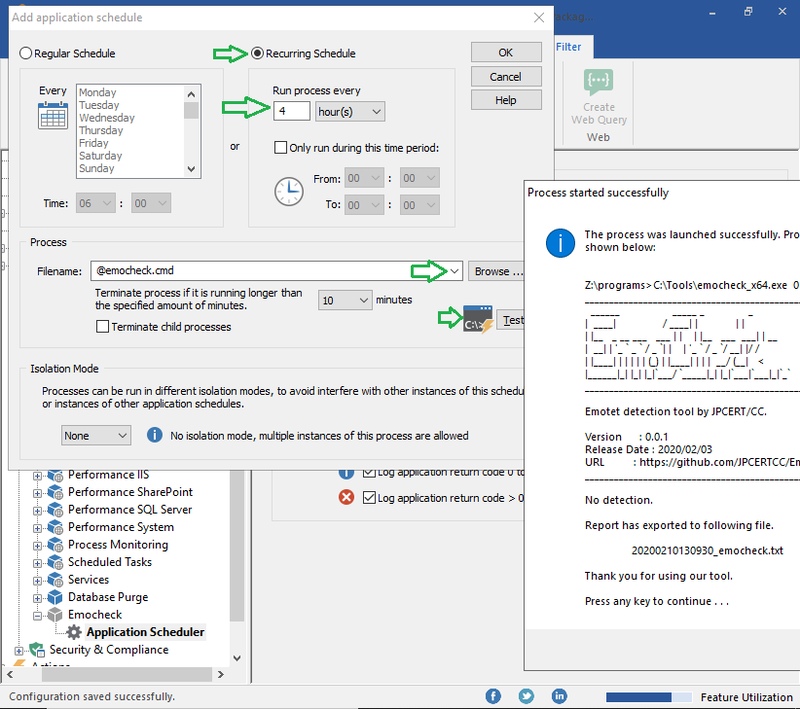
In the Application Scheduler dialog, click on the "+" button and specify a schedule; in this case, the tool is set to run every 4 hours. In the Process area click the dropdown menu in the Filename field and select the recently created script. Note that all embedded scripts start with the @ symbol. Click the Test button to check the output.
Fig.5: Configuring Application Scheduler
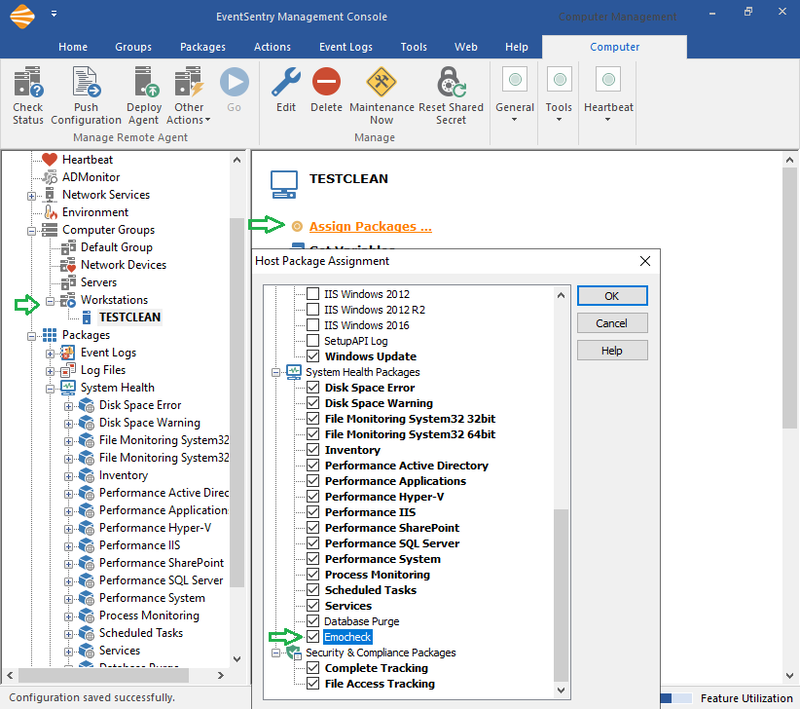
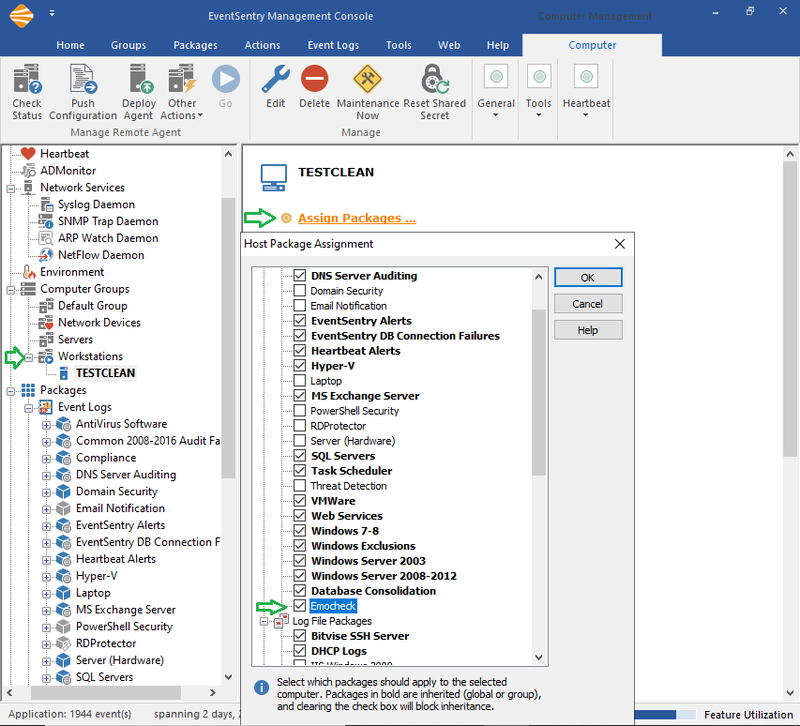
Either set the package global or assign it to the group(s) or computer(s) where the tool to should run.
Fig.6: Assigning Package
Creating an Alert
Before we create an event action, navigate to "Packages" and Right-click on Event Logs and select "Add Package". Again, assign a descriptive name (e.g. "Emocheck").
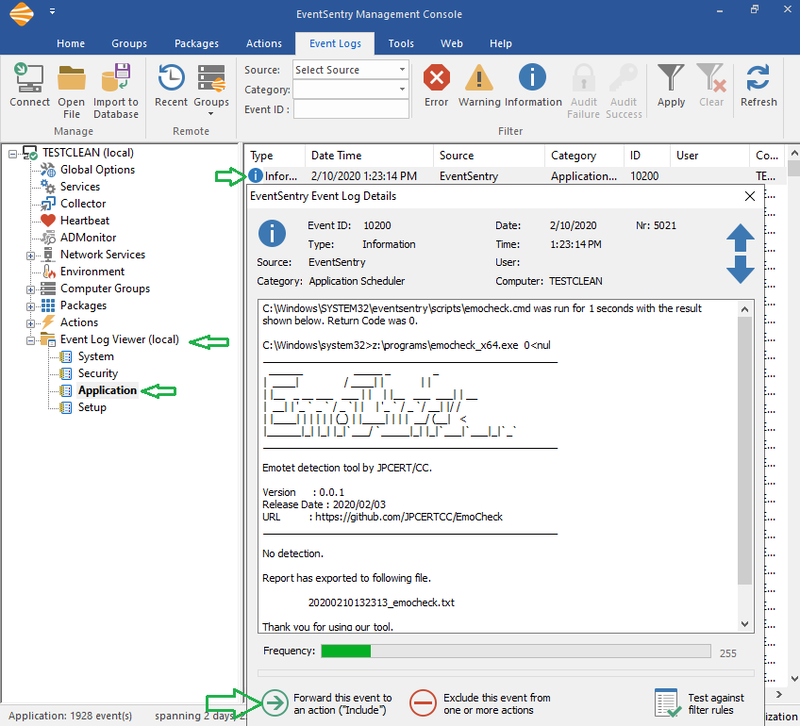
Since the Application Scheduler package is active and assigned, you should find the result in the local Application Log (package must be assigned to the local machine where EventSentry Server is running). Under Event Log Viewer (local) / Application, search for an event with event source EventSentry and ID 10200. Double-click the event to verify that it's showing the Emocheck output and click "Forward this event to an action ("Include")".
Fig.7: Creating an event action
*Note: You can temporarily set the application schedule to a short interval (e.g. 1 minute) to test and make sure it’s being executed correctly. Once you verified that it’s running properly, set the schedule back to the original interval. *
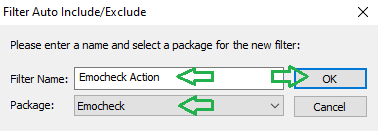
Then, click on "Forward this event to an action ("Include")", specify the name of the filter, select the package that we just created and click OK.
Fig.8: Creating an event action
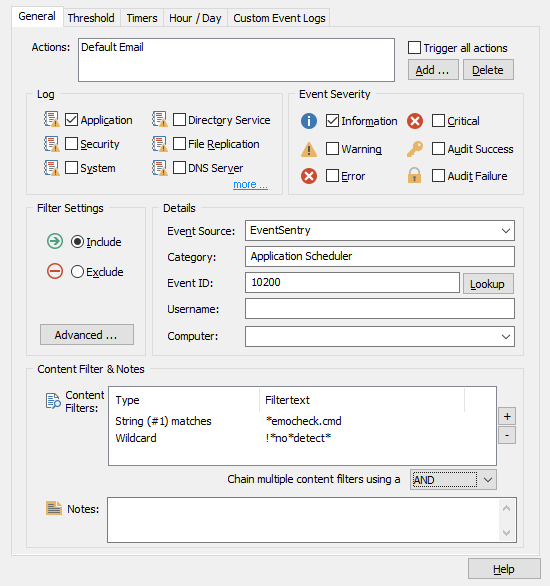
In the action field of the event filter, select the action(s) (e.g. “Default Email” to receive an email when this alert is triggered). Since the automatically created filter will match any event logged by the application scheduler, the content filter can be utilized to only match events that pertain to the emocheck utility.
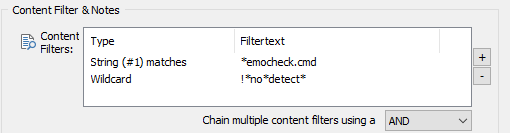
Add the following two content filters and select "AND" as "Chain multiple content filters using":
Fig.9: Filters
· The first entry will match the script name, so we don’t match events from other scripts (do not forget the leading * character)
· The second condition matches any output that DOES NOT contain "no detect". The "!" symbol before the wildcard negates the filter condition that follows.
The filter should look like this:
Fig.10: Filter window
Then, assign the event log package (identically to how the system health package was assigned) and save the configuration.
Fig.11: Assigning package to computer(s)
Note: To test the alert, delete the "!" symbol so the filter will match the normal output from emocheck. You should receive an email after the emocheck script runs.