Built for Humans
Powerful SIEM to help meet CMMC security requirements
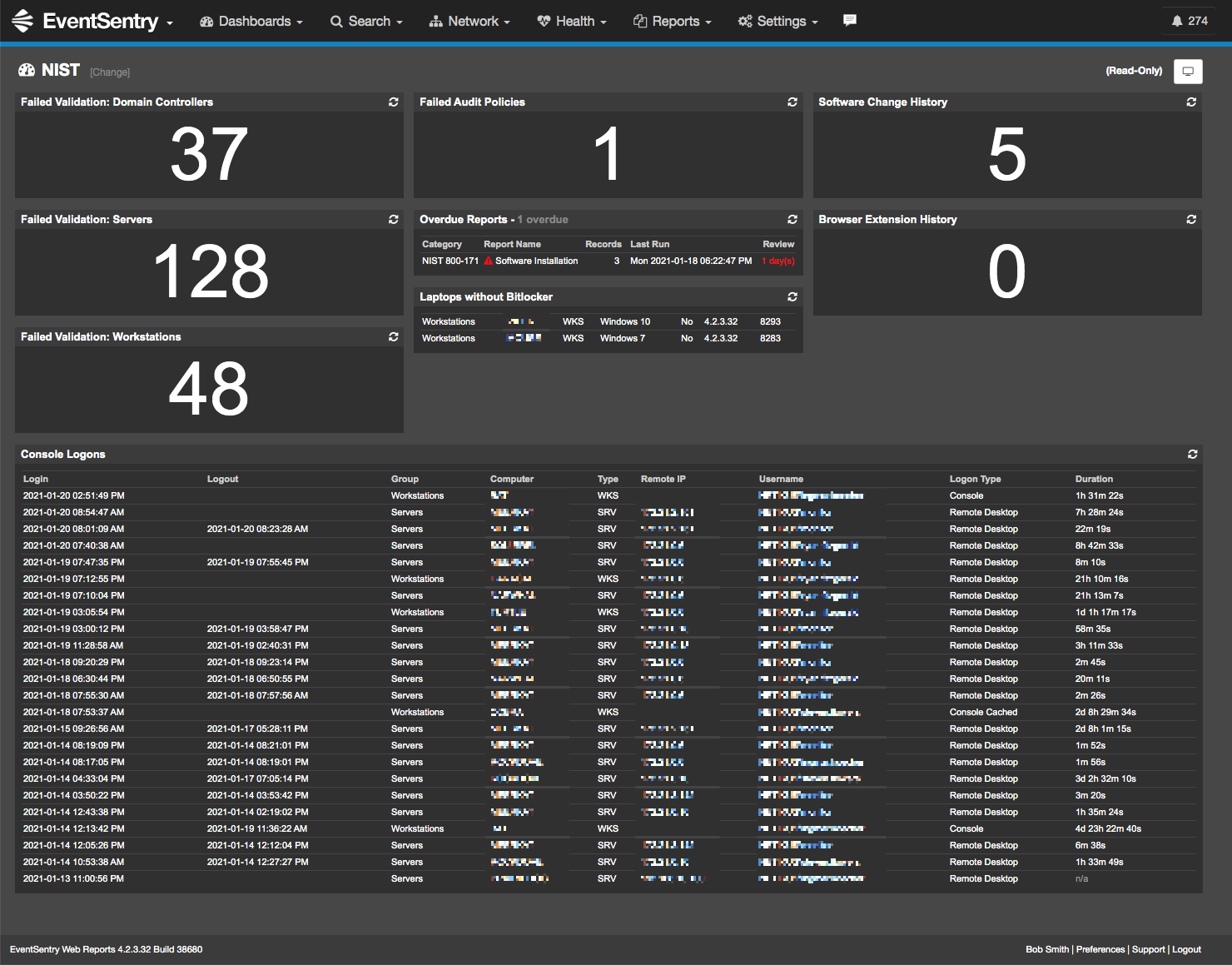
Flexible Dashboards
Customized for NIST / CMMC, help you keep an eye on important metrics to ensure you stay compliant.
Reporting
Includes ready-to-run compliance reports that can be scheduled, emailed or run on-demand.
Full SIEM
EventSentry includes log, FIM, AD & network traffic monitoring - in one single product.
Security
Alert on suspicious processes, malicious network activity, port scans and more.
Validation
Validate security settings across your entire Windows network against required and recommended settings.
Bonus
EventSentry also offers a complete software, hardware inventory along with health monitoring.
Don't miss key NIST / CMMC events on your network!
"In a day and age where everything has a maintenance agreement, this is one of the few that stand out as being genuinely worthwhile. The technician support is fantastic, the updates are regular and timely, and the product works like it is supposed to." >> READ MORE
Jamie H. (Director of IS&T, HIPAA Security Officer, PrimeWest Health)
"EventSentry’s multifaceted feature set has helped NMFTA predict and avoid Windows Server® crashes, Microsoft® SQL Server® failures, configuration problems in its VMware® environment, and malicious attacks against workstations and servers." >> READ MORE
Urban Jonson (CTO of NMFTA)
Perpetual License
You own the license
No Data Limit
Avoid unexpected costs
No Sensor Limit
Full visibility of your network
What is CMMC v2.0?
The Cybersecurity Maturity Model Certification (CMMC) program enhances cyber protection standards for companies in the DIB. It is designed to protect sensitive unclassified information that is shared by the Department with its contractors and subcontractors. The program incorporates a set of cybersecurity requirements into acquisition programs and provides the Department increased assurance that contractors and subcontractors are meeting these requirements.
The framework has three key features:
- Tiered Model: CMMC requires that companies entrusted with national security information implement cybersecurity standards at progressively advanced levels, depending on the type and sensitivity of the information. The program also sets forward the process for information flow down to subcontractors.
- Assessment Requirement: CMMC assessments allow the Department to verify the implementation of clear cybersecurity standards.
- Implementation through Contracts: Once CMMC is fully implemented, certain DoD contractors that handle sensitive unclassified DoD information will be required to achieve a particular CMMC level as a condition of contract award.
Self-Assessments are no longer enough
Full visibility within reach
EventSentry starts with a powerful baseline configuration and makes it easy to expand to the specifics of your environment.
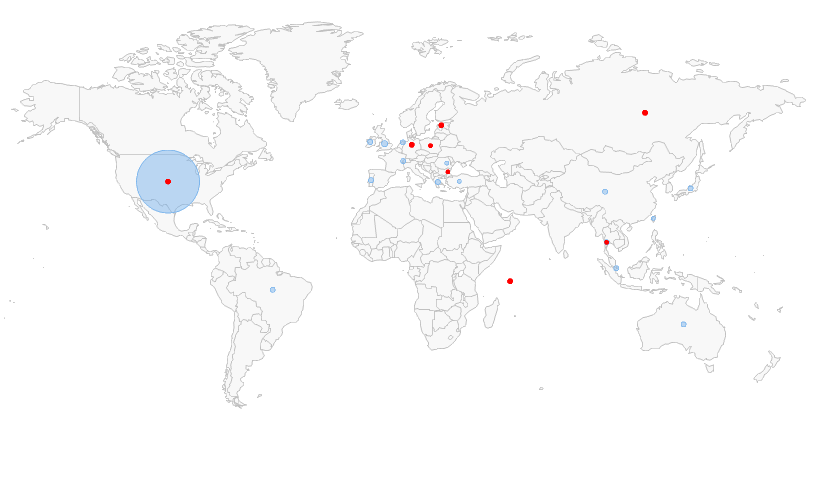
Easily spot outliers
Geo-locate threats
Automatically respond in real-time
Affordable CMMC Compliance Software
-
Start an evaluation
FREE fully functional for 30-days
-
Install EventSentry
Quick installation / Monitor in minutes
-
Become & Remain Compliant
Peace of mind included