How to monitor/detect PrintNightmare CVE-2021-1675 / CVE-2021-34527 utilizing the Windows Event Log and Sysmon
Article ID: 458
Category: Monitoring
Applies to: 4.x and later
Updated: 2021-07-07
Sysmon is a free driver-based utility that supplements Windows's built-in audit capabilities. Combining Sysmon with EventSentry's monitoring capabilities enables users to detect a number of potential threats on their monitored servers and workstations. The required Sysmon configuration file is attached below.
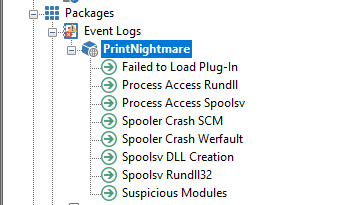
This article includes a pre-made Event Log Filter package with the required filters for detecting suspicious activity on Windows Print Spooler to alert of a possible Remote Code Execution Vulnerability (known as PrintNightmare, CVE-2021-1675).
To start using PrintNightmare filter rules, follow the steps below:
- Deploy Sysmon to all systems that are utilizing these rules. See KB 437 on how to automatically deploy (and/or configure) Sysmon with EventSentry (required Sysmon configuration file is attached below and available on GitHub).
- Download the .reg package below or from GitHub.
- Import the package in the management console. Click on "Packages", select "Import" and select the previously downloaded package.
- Select the package "PrintNightmare" from the list.
- Review the package properties (select package, click Properties) and make sure that the correct action is referenced.
- From the ribbon, click "Home" and then "Save" (or "Save & Deploy") to save the configuration.
Event Log Package for PrintNightmare
Sysmon configuration file