How can I discover all vulnerable Log4J libraries on my network?
EventSentry includes the validation script Threat-Intel: Log4j Remote Code Execution which will scan the local file system of any monitored host and find and report on all vulnerable Log4J instances.
Follow the steps below to activate the script and deploy it on your network.
Deployment
1. Open the Management Console, navigate to "Scripts" and ensure that scripts are up to date.
2. Add a new package under "Packages - Validation Scripts" and assign it to all hosts where the script should run.
3. Add a validation script object to the package and add the threat-intel tag. This will add the Log4J and other threat intel scripts. Add the database where the results should be stored in.
4. Save / Deploy the configuration.
Now wait 5-10 minutes for the script to be deployed, executed and the results to be available in the database.
View Results
1. In the Web Reports, navigate to "Health - Validation Scripts - Status".
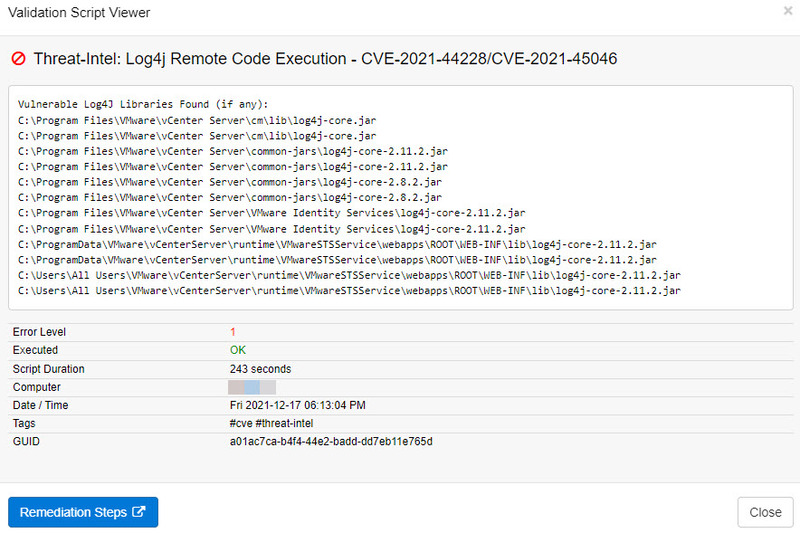
2. In the "Scripts" area, click "Show All" and click on the "Threat-Intel: Log4j Remote Code Execution - CVE-2021-44228/CVE-2021-45046" script.
3. In the "Passed" area, click "No".
4. Click on "Details" to see all hosts where a vulnerable Log4J library was found.
5. For each row, click the script name to view details.
Important Info when utilizing the PowerShell Security event log package
If you are utilizing the PowerShell Security event log package and are monitoring Windows Server 2012 R2 and earlier then you will need to disable the Suspicious Command Params filter in that package if it is configured to terminate the process. If you are only monitoring Windows Server 2016 and higher then you can simply download the latest packages which will automatically permit all PowerShell scripts launched by the EventSentry agent.
FAQ:
Q: What are these files that the script is listing in the results?
A: The script will list any known-bad executable .jar files that contain the Log4j vulnerability. Since these are executable files, they should be removed to prevent unwanted or unauthorized execution and prevent the vulnerability from being exploited or introduced. If you've already removed the files, the next time that the script runs it will update the results to indicate any remaining vulnerable files or to indicate a successful result.
Q: I receive an "access denied" error as part of the script result, what does this mean?
A: There are files or folders that could not successfully be checked for vulnerability. Please make sure the LocalSystem account does not have Deny rights on folders that need to be scanned for vulnerable files.
Q: I receive a "The batch file cannot be found" error as part of the script result, what does this mean?
A: This error only occurs when script was deleted while it was still executing. If you did not manually terminate the script, please ensure that your antivirus or antimalware products do not interfere with the "c:\windows\system32\eventsentry\scripts" folder.